The Infamous 8 eBook: Infrastructure as code (IaC) vulnerabilities to find and fix
Secure applications are one (huge) part of the cybersecurity landscape, but what about the code that hosts them? This vital cloud infrastructure needs to be air-tight as well, and it’s a worrying extension of the attack surface that could be exploited.
If you’re new to cloud server environments and how to secure them, then this guide will help you start your journey.
Your challenges are ready: it’s time to slay the Secure Code Warrior top 8 IaC security vulnerabilities.
- Learn about the most prominent cloud infrastructure security vulnerabilities
- Go in-depth with each vulnerability, learning how they work and how you can stop them from entering your code
- Test your skills by completing secure coding challenges via our gamified training arena.
- Play in your preferred IaC language: Kubernetes, Ansible, Docker, CloudFormation, or Terraform!
LEVEL UP YOUR SKILLS
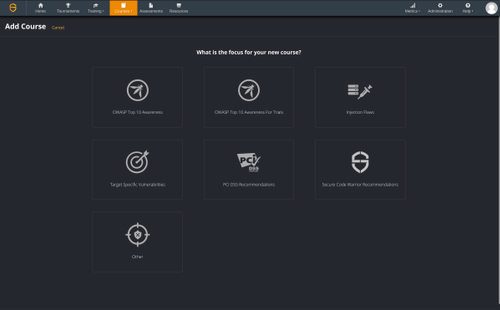
Uplift your secure code skills systematically with 100% hands-on training in how to spot and fix vulnerabilities, in your choice of programming language and frameworks.
Build upon your experiences and skillset with the Secure Code Warrior skills platform and move beyond passive recall to active application of your knowledge. This unique preventative approach will help make security an intrinsic part of your thought process and workflow to produce quality software - fast!
Build upon your experiences and skillset with the Secure Code Warrior skills platform and move beyond passive recall to active application of your knowledge. This unique preventative approach will help make security an intrinsic part of your thought process and workflow to produce quality software - fast!